BioEncrypt Mobile SDK
BioEncrypt is an open source mobile security project that is free to use and can be integrated into any mobile application. BioEncrypt uses TrustScores generated from over 30 behavioral biometric and device integrity data-points to create unbreakable encryption keys. TrustScores normalize security posture across diverse devices and users by selecting an authentication method proportionate to the risk. Trusted machine learning data is employed to create unbreakable encryption keys based on “who you are”. These keys can transparently authenticate a user during periods of high trust, such as familiar location, access time, or Bluetooth device.
Adaptive Authentication
Trust Measurements normalize security posture across devices and users enabling consistent enforcement of security in diverse environments.
Prevents decryption when a high risk device or user exceeds the threshold
Risk-based authentication requirements
Transparently authenticates users when the device and user are trusted
Combination of high-entropy factors create a cryptographically secure solution
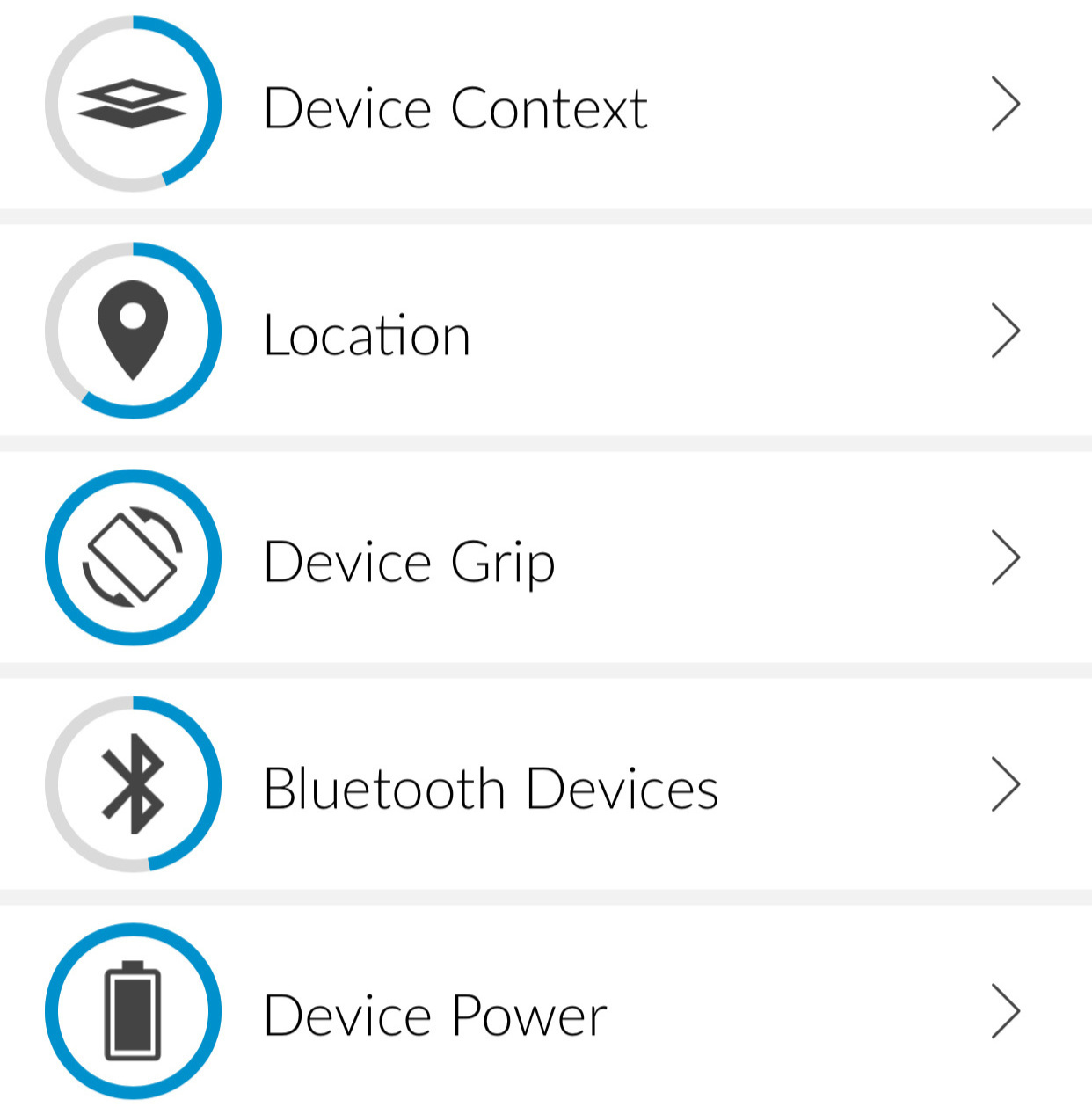
Trustfactors
Device TrustFactors identify unsafe data access environments resulting from platform or app issues. These factors predict the probability of data breach due to system or app integrity violation.
TrustFactors are classified by user, device, and category (WiFi, motion, location, etc)
Shared, asynchronous datasets collection maximizes performance across large numbers of TrustFactors
Currently 30+ TrustFactors
Decay metrics modulate learning speed and accuracy
TrustFactor can be enable/disable
Weights and thresholds are modifiable
Modify risk thresholds for user/device
Turn TrustFactors on or off
Increase/decrease associated penalties
You are the password
User TrustFactors profile user access to identify the probability of physical attack, theft, or abuse. These factors predict the probability of device theft/loss due to the user environment.
BioEncrypt dynamically generates encryption keys from TrustFactors when the TrustScore exceeds the defined threshold.
Combination of high-entropy factors create a cryptographically secure solution
Discovery of transparent keys is an impossible exercise stronger than any other form of authentication
Encryption keys are combined with device TrustFactors to “lock-in” secure states
Authentication can be cryptographically invalidated if the device becomes high-risk
Adaptive Authentication
The BioEncrypt SDK output provides the application intelligence to select an authentication modality that corresponds to the identified level of user and device risk. This assessment is typically performed during initial application access and prior to any form of authentication. For example, a user that is exhibiting untrusted behavior, such as traveling to another country, would be considered a low-trust user. A user that exhibits known and predictable behaviors, such as accessing the application from their home Wi-Fi while connected to a known Bluetooth device, could be transparently authenticated used encryption keys derived from these trusted data points.
Patented Cryptographic Scheme
BioEncrypt creates keys that embody learned and trusted behaviors. Hundreds of keys exist that cannot be decrypted unless the user exhibits the same trusted behavior. This method results in “passwords” that are not compromised of something you have or know, it is who you are.
System for transparent authentication across installed applications (US9477825B1 , US9992023B2)